Having fun with RISK management equations
Have past a few weeks without any post, so, I think it's the time... Today, I'm havin' fun with MS Excel (yes, I'm a f**ck1ng n00b in Excel) calculating and automating some equations for the risk assessment methodology I've created for a company.
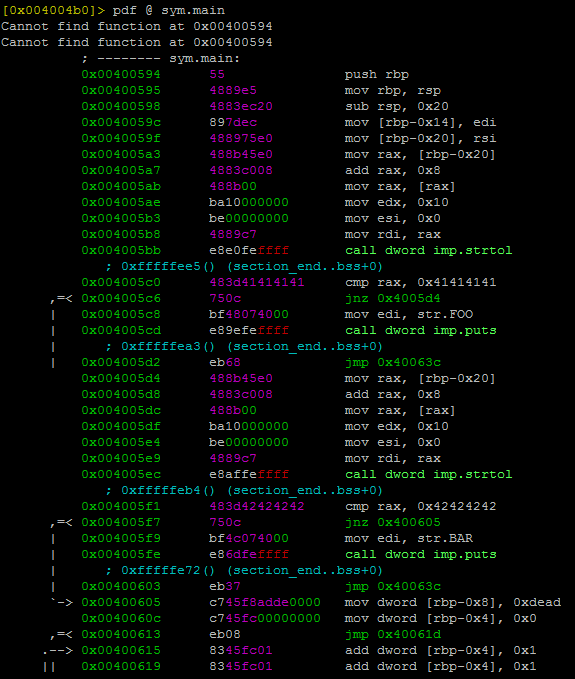
Example of threat evaluation (taken from the Internet):
The methodology that we created as a team, includes the basic principles of risk management. I've used some references such as NIST-800-30 special publication (Risk Management Guide for Information Technology Systems), ISO/IEC 27005:2008 Information technology - Security techniques - Information security risk management and many others documents widespread on the Internet !
Finally, a few moments ago I optimized an excel formula to automate the process of THREATS valuation using their impacts and likelihoods. First, I tried this one:
=IF(AND(C4=1,D4=1),1,
IF(AND(C4=2,D4=1),1,
IF(AND(C4=3,D4=1),2,
IF(AND(C4=1,D4=2),1,
IF(AND(C4=2,D4=2),2,
IF(AND(C4=3,D4=2),3,
IF(AND(C4=1,D4=3),2,
IF(AND(C4=2,D4=3),3,
IF(AND(C4=3,D4=3),3,0)))))))))
But... It's too long, and excel sends u a syntax error. So, I exercised my mind and I could make it easier taking leverage of the boolean operators OR() and AND() as well as nested IF() statements.
=IF(OR(
AND(C4=1,D4=1),
AND(C4=2,D4=1),
AND(C4=1,D4=2)),1,
IF(OR(
AND(C4=3,D4=1),
AND(C4=2,D4=2),
AND(C4=1,D4=3)),2,
IF(OR(
AND(C4=3,D4=2),
AND(C4=2,D4=3),
AND(C4=3,D4=3)),3,0)))
Works fine !, not a big deal though. As you can see, this is something VERY VERY simple, but I'm pr0ud of my newbie Excel Skillz jajaj :D...
Have fun ! ;)
Example of threat evaluation (taken from the Internet):
The methodology that we created as a team, includes the basic principles of risk management. I've used some references such as NIST-800-30 special publication (Risk Management Guide for Information Technology Systems), ISO/IEC 27005:2008 Information technology - Security techniques - Information security risk management and many others documents widespread on the Internet !
Finally, a few moments ago I optimized an excel formula to automate the process of THREATS valuation using their impacts and likelihoods. First, I tried this one:
=IF(AND(C4=1,D4=1),1,
IF(AND(C4=2,D4=1),1,
IF(AND(C4=3,D4=1),2,
IF(AND(C4=1,D4=2),1,
IF(AND(C4=2,D4=2),2,
IF(AND(C4=3,D4=2),3,
IF(AND(C4=1,D4=3),2,
IF(AND(C4=2,D4=3),3,
IF(AND(C4=3,D4=3),3,0)))))))))
But... It's too long, and excel sends u a syntax error. So, I exercised my mind and I could make it easier taking leverage of the boolean operators OR() and AND() as well as nested IF() statements.
=IF(OR(
AND(C4=1,D4=1),
AND(C4=2,D4=1),
AND(C4=1,D4=2)),1,
IF(OR(
AND(C4=3,D4=1),
AND(C4=2,D4=2),
AND(C4=1,D4=3)),2,
IF(OR(
AND(C4=3,D4=2),
AND(C4=2,D4=3),
AND(C4=3,D4=3)),3,0)))
Works fine !, not a big deal though. As you can see, this is something VERY VERY simple, but I'm pr0ud of my newbie Excel Skillz jajaj :D...
Have fun ! ;)

Siempre hay una primera vez en algo, juas, aunque la destresas de programcion que has adquirido se vieron reflejadas en este pequeño pero laborioso ejercicio.
ResponderEliminarDe la manera convencional y sin estar usando los operadores if & or, hubiera sido demaciado tedioso y un mega chorisote de codigo.
-saludos-
Risk = Hazard.Probability.Exposure = liklihood.Danger
ResponderEliminar