DotDotPwn - The Directory Traversal Fuzzer
"Welly, welly, welly, well." -- A Clockwork Orange (movie).
Hell Yes !!!! B-), a few weeks ago, my brother chr1x from CubilFelino Security Labs (published a tool to detect directory traversal vulnerabilities in FTP/HTTP servers. It only relied upon 2 .txt files (databases) with the payloads to be lauched to the target. Then, some cool ideas came into my mind, so, I wrote the c0de from the skratch and in a modular basis, as well as, I included a lot of features/enhacements, but the main change was the pass from being a Checker to a Fuzzer (I c0ded a Traversal Engine for it).
Well, Stay tuned for the public release ;) s00n !! (DotDotPwn v2.0)
Official Website: http://chr1x.sectester.net/toolz/ddpwn/
----------
Release date: 2/Sept/2010 (NON-PUBLIC Version)
Author: nitrØus (nitrousenador@gmail.com)
Changes / Enhancements / Features:
* From Checker to Fuzzer
* Rewritten from the scratch
* Modular architechture (DotDotPwn packages)
* Traversal Engine to automatically create the fuzzing patterns to be sent.
This engine makes all the permutations between the dots and slashes
encodings, iterates the number of deepness passed as argument and finally,
it concatenates the filenames intelligently according to the Operating System
detected (in case of -O switch enabled), otherwise, the engine includes all
the defined file sets (Windows, UNIX and Generic).
* -O switch for Operating System (nmap) and -s switch for service detection
* -f switch available to define a specific file name to retrive
* -U and -P switches to supply specific usernames/passwords
* -d switch to specify the desired deep of traversals
(e.g. deep 3 equals to ../../../)
* -t switch to specify the time in milliseconds between each attemp
* -x switch to specify a different TCP/UDP port than the defaults
* -b switch to break after the first vulnerability is found
* -q switch for quiet mode (doesn't print each attemp in STDOUT)
* Special treatment of Slash/Backslash in filenames in order to have a
correct semantic within each traversal string.
* Improvement in the FTP module to compare against the server's response code
instead of vendor-dependent response message (in compliance with RFC 959 FTP)
* Improvement in the parameter passing
* A cool banner was included ;)
Supported modules:
- HTTP
- HTTP Parameters (url)
- FTP
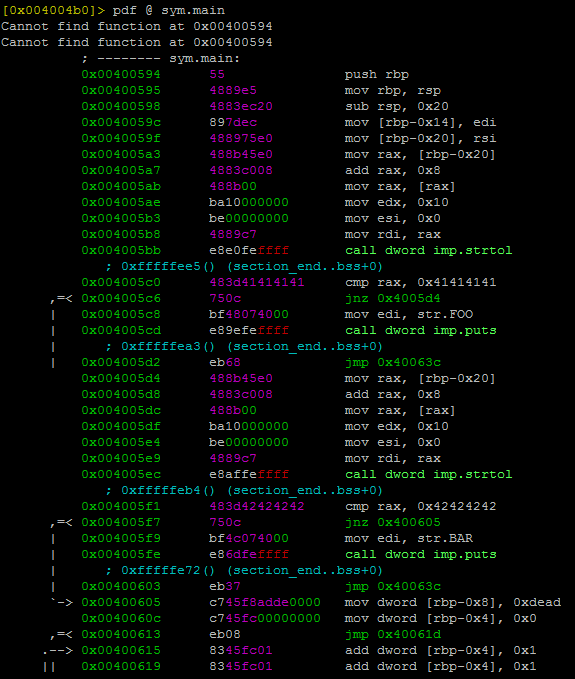
And as I said before, a picture is worth a thousand words, I post some screenshots ;) .. Enjoy them !
DotDotPwn (Usage)

Traversal Engine (Description)

Traversal Engine (Resources)

Traversal Engine (Working [internals])

OS and Service detection (taken into account in the Traversal Engine for intelligent fuzzing)

HTTP-Params Module (Description)

HTTP-Params Module (Usage)

HTTP-Params Module (Vulnerabilities found)

FTP Module (Vulnerabilities found, quiet mode and retrieved files)

HTTP Module (Vulnerabilities found)

Well, stay tuned on http://chr1x.sectester.net/toolz/ddpwn/ for the public release ;).
Keep Fuzz1ng !!!!!! B-/
nitrØus
Hell Yes !!!! B-), a few weeks ago, my brother chr1x from CubilFelino Security Labs (published a tool to detect directory traversal vulnerabilities in FTP/HTTP servers. It only relied upon 2 .txt files (databases) with the payloads to be lauched to the target. Then, some cool ideas came into my mind, so, I wrote the c0de from the skratch and in a modular basis, as well as, I included a lot of features/enhacements, but the main change was the pass from being a Checker to a Fuzzer (I c0ded a Traversal Engine for it).
Well, Stay tuned for the public release ;) s00n !! (DotDotPwn v2.0)
Official Website: http://chr1x.sectester.net/toolz/ddpwn/
----------
Release date: 2/Sept/2010 (NON-PUBLIC Version)
Author: nitrØus (nitrousenador@gmail.com)
Changes / Enhancements / Features:
* From Checker to Fuzzer
* Rewritten from the scratch
* Modular architechture (DotDotPwn packages)
* Traversal Engine to automatically create the fuzzing patterns to be sent.
This engine makes all the permutations between the dots and slashes
encodings, iterates the number of deepness passed as argument and finally,
it concatenates the filenames intelligently according to the Operating System
detected (in case of -O switch enabled), otherwise, the engine includes all
the defined file sets (Windows, UNIX and Generic).
* -O switch for Operating System (nmap) and -s switch for service detection
* -f switch available to define a specific file name to retrive
* -U and -P switches to supply specific usernames/passwords
* -d switch to specify the desired deep of traversals
(e.g. deep 3 equals to ../../../)
* -t switch to specify the time in milliseconds between each attemp
* -x switch to specify a different TCP/UDP port than the defaults
* -b switch to break after the first vulnerability is found
* -q switch for quiet mode (doesn't print each attemp in STDOUT)
* Special treatment of Slash/Backslash in filenames in order to have a
correct semantic within each traversal string.
* Improvement in the FTP module to compare against the server's response code
instead of vendor-dependent response message (in compliance with RFC 959 FTP)
* Improvement in the parameter passing
* A cool banner was included ;)
Supported modules:
- HTTP
- HTTP Parameters (url)
- FTP
And as I said before, a picture is worth a thousand words, I post some screenshots ;) .. Enjoy them !
DotDotPwn (Usage)

Traversal Engine (Description)

Traversal Engine (Resources)

Traversal Engine (Working [internals])

OS and Service detection (taken into account in the Traversal Engine for intelligent fuzzing)

HTTP-Params Module (Description)

HTTP-Params Module (Usage)

HTTP-Params Module (Vulnerabilities found)

FTP Module (Vulnerabilities found, quiet mode and retrieved files)

HTTP Module (Vulnerabilities found)

Well, stay tuned on http://chr1x.sectester.net/toolz/ddpwn/ for the public release ;).
Keep Fuzz1ng !!!!!! B-/
nitrØus
Chida la herramienta wey, buenas ideas..
ResponderEliminar