Buscar este blog
Yet another security blog with random() shit done by yet another guy in the infosec industry based in Mexico.
Entradas
Mostrando entradas de octubre, 2010
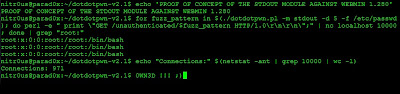
DotDotPwn v2.1 - The Traversal Directory Fuzzer
- Obtener enlace
- Correo electrónico
- Otras aplicaciones