IOActive Labs Research: Striking Back GDB and IDA debuggers through malfor...
IOActive Labs Research: Striking Back GDB and IDA debuggers through malformed ELF executables
By Alejandro Hernández @nitr0usmx
By Alejandro Hernández @nitr0usmx
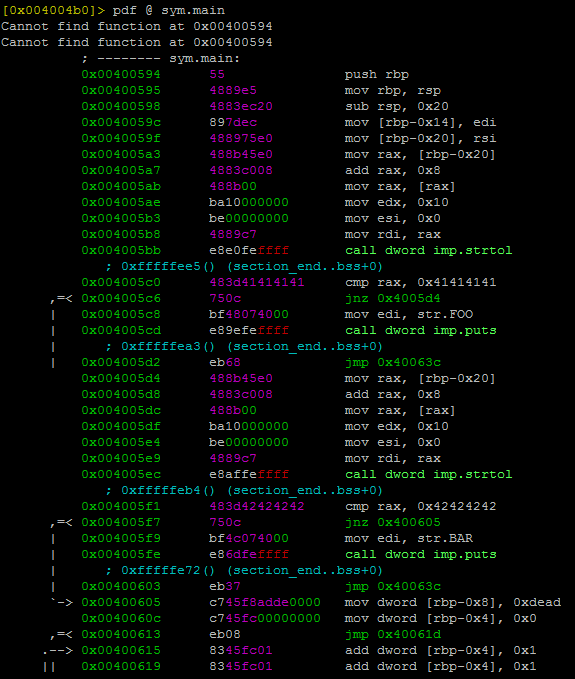
Day by day the endless fight between the bad guys and good guys mostly depends on how fast a countermeasure or anti-reversing protection can be broken. These anti-reversing mechanisms can be used by attackers in a number of ways: to create malware, to be used in precompiled zero-day exploits in the black market, to hinder forensic analysis, and so on. But they can also be used by software companies or developers that want to protect the internal logic of their software products (copyright).
The other day I was thinking: why run and hide (implementing anti-reversing techniques such as the aforementioned) instead of standing up straight and give the debugger a punch in the face (crashing the debugging application). In the next paragraphs I’ll explain briefly how I could implement this anti-reversing technique on ELF binaries using a counterattack approach.
...
Comentarios
Publicar un comentario